Following the global incident that affected Windows systems during the day of July 19, CrowdStrike issued a status report and confirmed that the event was not a cyberattack. According to some estimates, this incident may have potentially impacted more than 55 million systems.
What happened?
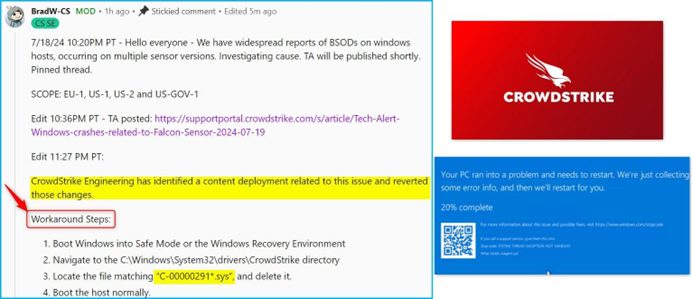
On July 19, 2024 at 04:09 UTC, CrowdStrike published a sensor configuration update for Windows systems. These updates are part of the protection mechanisms of the Falcon platform. This specific update triggered a logic error, resulting in a system crash and Blue Screen of Death (BSOD) on the affected systems. The problematic update was quickly corrected at 05:27 UTC the same day.
Customers running Falcon Sensor for Windows version 7.11 and above, who were online between Friday, July 19, 2024 at 04:09 UTC and Friday, July 19, 2024 at 05:27 UTC, may be affected.
Systems running Falcon Sensor for Windows 7.11 and later that downloaded the updated configuration between 04:09 UTC and 05:27 UTC were susceptible to a system crash.
Introduction to the configuration file
The configuration files mentioned above are referred to as " channel files" and are part of the behavioral protection mechanisms used by the Falcon Sensor. Channel file updates are a normal part of sensor operation and occur multiple times per day in response to new tactics, techniques, and procedures discovered by CrowdStrike. This is not a new process; the architecture has been in place since Falcon was created.
Steps of the issue
- Update deployment:
- Date and time: July 19, 2024, 04:09 UTC.
- Action: Publication of a sensor configuration update for Windows systems.
- Objective: The update was designed to improve detection of malicious named pipes used by C2 frameworks in cyberattacks.
- Logic error triggered:
- Effect: The update caused a logic error, resulting in an operating system crash (BSOD) on affected machines.
- Impacted file: Channel File 291.
- CrowdStrike's response:
- Date and time: July 19, 2024, 05:27 UTC.
- Action: Rapid correction of the configuration update to resolve the logic error.
Technical details
- Configuration file location:
- Directory: C:\\Windows\\System32\\drivers\\CrowdStrike\\
- Naming format: Configuration files starting with "C-" and ending with .sys.
- Identification of the impacted file:
- File: Channel File 291.
- Full name: "C-00000291-.sys".
- Function: Controls the evaluation of named pipe execution on Windows systems.
- Faulty update:
- Content: The update aimed to target malicious named pipes used by C2 frameworks.
- Logic error: The update triggered a logic error, causing the operating system to crash.
- Remediation:
- Fix: Update to the contents of Channel File 291 to correct the logic error.
- No additional changes: No further changes to the file beyond the corrected logic.
Impact
- Affected systems:
- Version: Falcon Sensor for Windows version 7.11 and above.
- Impact window: Systems online between 04:09 UTC and 05:27 UTC on July 19, 2024.
- Consequences:
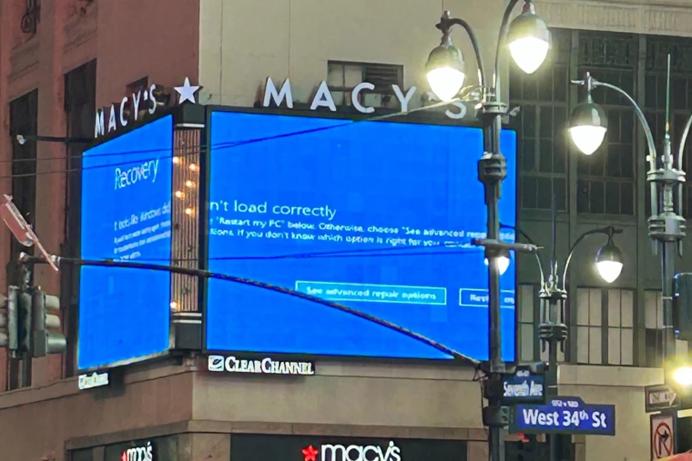
- System crashes: Affected systems experienced BSODs, leading to service interruptions.
- Service disruption: Operations were impacted at various financial institutions and businesses.

Associated risks
- Service disruption:
- Impacted sectors: Several financial institutions, technology companies, and other professional users.
- Immediate effects: Blue Screen of Death (BSOD), operational interruptions, potential delays, and productivity loss.
- How configuration files work:
- Channel Files: Integral parts of Falcon's behavioral protection mechanisms, regularly updated.
- Location: C:\\Windows\\System32\\drivers\\CrowdStrike\\
- Identification: The specific file impacted starts with "C-00000291-" and ends with .sys.
- Logic error:
- Cause: The configuration update targeting malicious named pipes triggered a logic error.
- Consequence: Operating system crash.
Consequences
- Service disruption:
- Impacted sectors: Financial institutions, technology companies, public services, and professional users.
- Immediate effects: BSOD, operational interruptions, delays, and productivity loss.
- Market reaction:
- Fluctuations: CrowdStrike's stock fell more than 10% in pre-market trading on the New York Stock Exchange. Microsoft's stock was also affected.
- Investor confidence: Reduced confidence due to the scale of the outage.
- Infrastructure stability:
- Unaffected infrastructure: Systems running Linux or macOS, and Windows systems not connected during the impact window.
- Continuous operations: Unaffected systems continue to operate normally without risk of encountering this event in the future.
Remediation and follow-up
- Update fix:
- Action: Correction of the logic error in Channel File 291.
- Status: No further modifications to the file beyond the logic correction.
- Customer support:
- Resources: CrowdStrike's blog and support portal for up-to-date remediation guidance.
- Contact: Support team available for customer-specific needs.
- Root cause analysis:
- Objective: In-depth analysis to understand how the logic error occurred.
- Commitment: Identify and implement fundamental or workflow improvements to strengthen the update process.
Future phishing risks
As a result of this incident, several domains have been created by malicious actors attempting to capitalize on the situation through phishing campaigns. Users should remain vigilant and monitor the following indicators of compromise (IOCs):
- crowdstrikebluescreen.com
- crowdstrike0day.com
- crowdstrike-bsod.com
- crowdstrikedoomsday.com
- crowdstrikefix.com
- crowdstrikedown.site
- crowdstriketoken.com
These domains may be used to spread misinformation, harvest sensitive data, or distribute malware. We strongly recommend that our users avoid visiting these sites and report any suspicious activity to our support team.
The July 19, 2024 incident, caused by a CrowdStrike sensor configuration update, highlighted the complex challenges that cybersecurity companies face in a constantly evolving technology landscape. Although this update led to system crashes and Blue Screens of Death (BSOD) potentially affecting more than 55 million Windows systems, CrowdStrike responded quickly by correcting the error in less than two hours. This incident, although significant, was not the result of a cyberattack but a logic error in the update, underscoring the critical importance of rigor and testing in software deployment processes.
However, the consequences of this event extend beyond immediate disruptions. Malicious actors quickly exploited the situation by creating phishing domains such as crowdstrikebluescreen.com and crowdstrikefix.com, aimed at deceiving users and potentially stealing sensitive information. CrowdStrike continues to conduct an in-depth analysis to understand the root causes of the error and implement improvements to prevent future incidents. The company also advises all users to remain vigilant against phishing attempts and to report any suspicious activity. This incident serves as a stark reminder of the need for constant vigilance and rapid response to maintain security and trust in global digital infrastructure.
Sources:
https://www.crowdstrike.com/blog/technical-details-on-todays-outage/

