SYLink AI: the model designed for cybersecurity and SOC operations
In a context where security operations centers face a continuous rise in attacks, an expanding monitoring surface, growing incident complexity and strong pressure on L1 and L2 teams, artificial intelligence becomes a structuring lever to strengthen detection, qualification and investigation. This is precisely where SYLink AI fits — our model dedicated to cybersecurity and SOC use cases.
SYLink AI was designed to address the concrete needs of corporate cyber teams: threat intelligence, incident response, vulnerability analysis, advanced detection, investigation, rule production, triage support and analyst assistance. Where general-purpose models often remain too broad, too imprecise or poorly suited to field reality, SYLink AI was built as a specialized AI, capable of understanding the operational logics of cyber defense and producing answers directly usable in a demanding operational environment.
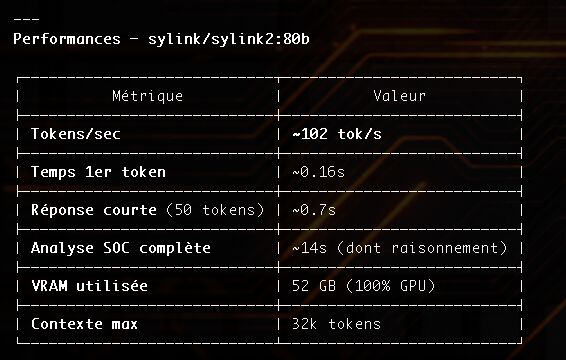
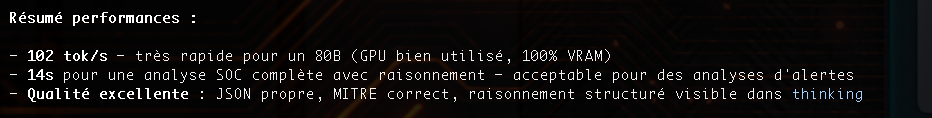
Developed by SYLink Technologie, SYLink AI relies, per your inputs, on a Mixture-of-Experts architecture of 80 billion parameters, with about 3 billion active parameters per token, native reasoning mode and tool-calling support. This approach reconciles depth of analysis, business specialization and execution efficiency. It aims to deliver high-level assistance to analysts on a variety of use cases: MITRE ATT&CK mapping, APT analysis, IOC correlation, attack-chain reconstruction, patch prioritization, creation of Sigma, YARA, Snort or Suricata rules, compliance support and executive summary for decision-makers.
The value of a specialized model like SYLink AI is not limited to "answering questions". In a modern SOC, the real challenge is to accelerate high-value tasks, reduce analysts' cognitive load and improve decision quality. The NATO / Armed Forces study on AI for detection shows that the most promising use cases today focus on analyst assistance, alert qualification, investigation, query generation, enrichment and, eventually, certain forms of supervised automation. It also points out that agentic AI is progressing particularly on the qualification and investigation phases, with a constant need for human control.
At SYLink, we hold this vision firmly: SYLink AI is not meant to replace analysts, let alone substitute for a CSIRT or a crisis cell. The CLUSIF recalls that a SOC is not just a piece of technology, but a complete operational organization, founded on documented processes, skilled human resources, fit-for-purpose tools and smooth integration with other security mechanisms. It also recalls that a SOC must not operate alone, nor be "dropped" onto the existing setup without integration. SYLink AI is thus positioned as an operational augmentation brick at the service of the SOC, not as an isolated black box.
This approach is essential because a credible cyber AI must integrate into the SOC's real processes: prevention, detection, reaction, security administration, watch, reporting, contextualization and continuous improvement. The CLUSIF stresses that detection only matters if linked to actionable rules, defined scenarios, escalation procedures and an associated response. An alert with no clear action consumes resources without creating value. This is where a model like SYLink AI takes its full meaning: helping turn raw information into actionable decisions, faster, cleaner and more consistently.
SYLink AI can thus assist SOC teams at multiple levels. For L1, it can accelerate triage, prioritization and rephrasing of alerts. For L2, it can enrich context, propose hypotheses, guide qualification and help reduce false positives. For expert teams, it can contribute to deep analysis, the construction of detection scenarios, the production of defense content or the synthesis of complex incidents. The CLUSIF notes that L1 analysts must stay focused on fast handling and L2 must concentrate their expertise on investigation, follow-up of corrective actions and continuous detection improvement.
But a specialized cyber AI cannot be credible without strong reflection on trust. The NATO / Armed Forces study highlights now well-known risks: data leakage, hallucinations, response variability, model poisoning, insufficient control over outputs or information sent to the model. It also emphasizes that hosting, model provenance and quality of the usage framework become decisive criteria, especially when AI intervenes in critical decision or automation processes. In this context, SYLink AI is built with a central requirement: control. Control of usage, control of data, control of hosting, control of outputs and maintenance of human control over important decisions.
This requirement maps directly onto the best practices recalled by the CLUSIF around the SOC's own security. A SOC must be protected for availability, confidentiality, integrity and traceability. Logging mechanisms must record the relevant events, prevent log tampering, protect log devices from unauthorized access and be regularly monitored. In other words, the AI assisting the SOC must itself sit within a robust, auditable and controlled security framework.
Along these lines, SYLink AI was designed to produce structured and useful outputs. For technical teams, it can provide detailed analysis, qualification hypotheses, MITRE mappings, containment leads, remediation recommendations or rule proposals. For managers and decision-makers, it can produce an executive summary, an exposure synthesis, a risk hierarchy and short-term and strategic recommendations. This ability to adapt to the audience's expectations is essential in a SOC environment where analysts, operators, CISOs, business owners and executive management coexist. The CLUSIF stresses the importance of reporting, indicators and dashboards to account for activity, demonstrate the system's performance and steer its maturity gain.
SYLink AI also fits a contextualization logic. A good SOC never works in a vacuum: it needs to know the monitored architecture, critical assets, production changes, patch state, CMDB elements, known vulnerabilities and business stakes. The CLUSIF insists on this need for context in order to correctly qualify an incident and propose relevant action plans. A dedicated cyber LLM takes its full value when it can reason on contextualized data, link an alert to a business perimeter, weight severity by the affected asset and help produce a truly useful response.
On the deployment side, the same realism logic must apply. The CLUSIF recommends a progressive rollout, starting with the most critical perimeters and the most relevant use cases, in order to obtain quick concrete results and avoid discrediting the project with too broad an ambition from day one. We share this conviction: adopting a cyber AI must not be a press-release stunt, but a structured, steered, measured trajectory aligned with real SOC needs.
Finally, SYLink AI fits a strictly defensive vision. It is designed to assist protection, detection, analysis and response — not to enable unauthorized offensive uses. This line is consistent with market expectations, with the trust stakes around specialized models, and with the evolution observed by the NATO / Armed Forces: automation is progressing, agentic AI is gaining ground, but the requirement for explainability, reproducibility and trust control remains central.
With SYLink AI, SYLink Technologie asserts a clear ambition: deliver an AI truly built for operational cybersecurity, capable of integrating into modern SOC practices, of assisting analysts without erasing them, of accelerating investigations without sacrificing rigor, and of providing a specialized response to a need that has become critical for organizations. More than a model, SYLink AI embodies a vision: that of a useful, controlled, contextualized cyber AI focused on field effectiveness.

